Beautiful Work Info About How To Start Snort

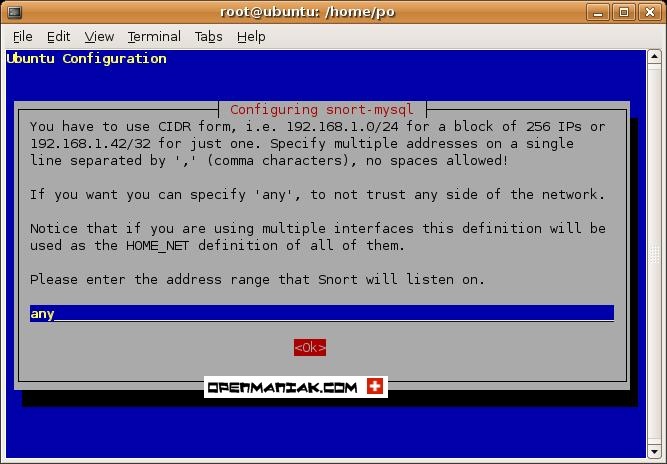
Snort will look at all sources.
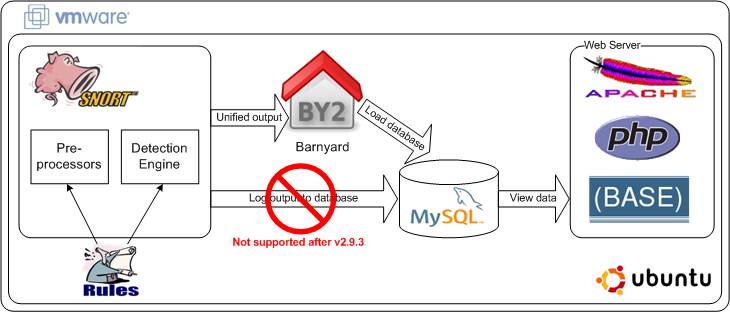
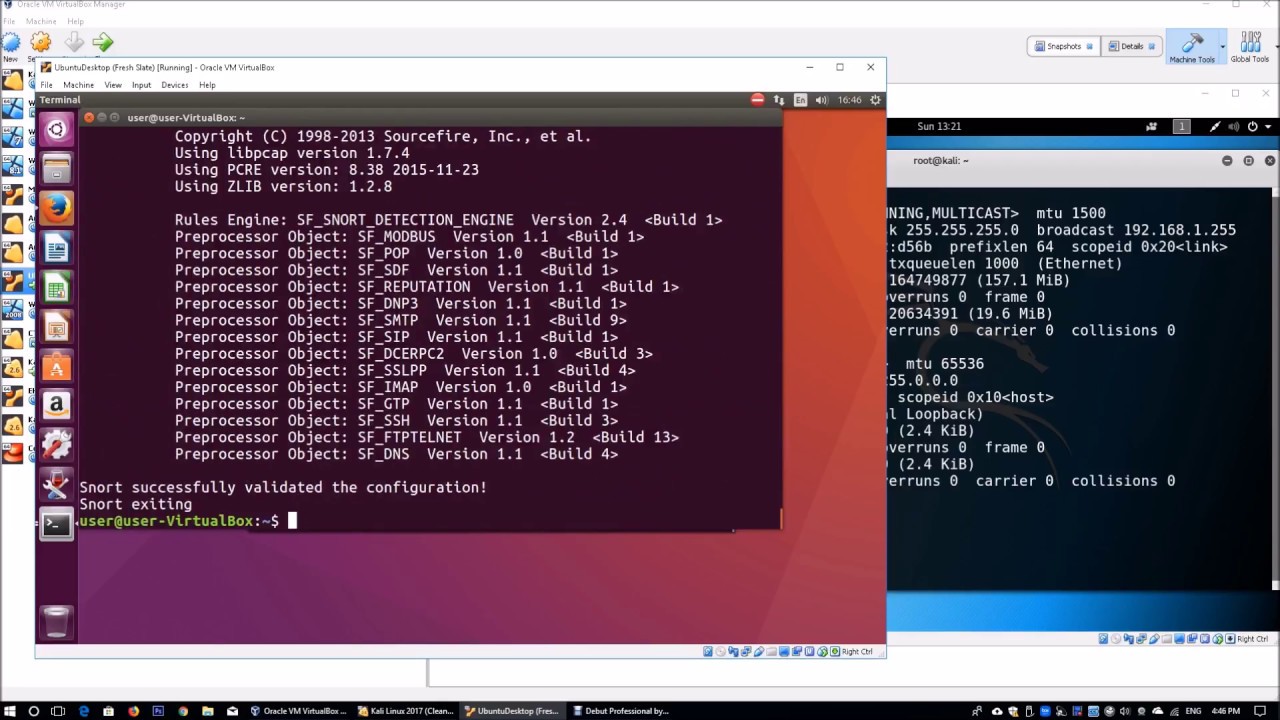
How to start snort. Setting up a basic configuration of snort on ubuntu is fairly simple but takes a few steps to. Setting up a basic configuration of snort on centos is fairly simple but. To get snort ready to run, you need to change the default configuration settings file (which is created as part of the snort installation) to match your local environment and operational.
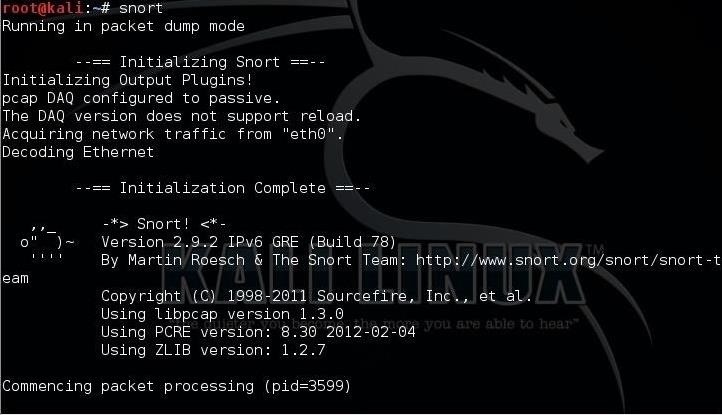
Click the icon (shown highlighted with a red box in the image below) to start snort. 1 snort is typically run from the cli (as simple as typing 'snort' in cmd) and when it starts successfully, you should see messages about the version, (running) mode, rules. Before you install snort, you need libpcap and libpcre’s respective.
To run snort, simply typ snort in the command prompt. To enable network intrusion detection (nids) mode (so that you don't record every single packet sent down the wire), try this : Here's how to do it from the sensor cli (ftd running on a firepower appliance in this case):
However, you probably want to run the program in the background so you can actually still use your server for other things. Extract the snort source code. You can now start snort.
The instructions that follow assume you have decided to install the latest version of snort on windows using the executable installer file available from the snort website. Download the latest snort free version from snort website. First, you will learn how to configure and.
Up to 50% cash back in this course, getting started with snort 3, you will learn foundational knowledge to operate snort and leverage its plugins. How do i run snort? How to install and run snort on windows.
This looks for a malicious x86 syscall that can be used to elevate privilege on linux kernel 3. 5 steps to install and configure snort on linux 1. I will also explain the basic structure of a snort rule and demons.
You should extract the latest file now. Snort has three primary uses: This rule looks for a malicious mmap on arm that targets an overflow.
Snort will generate an alert when the set condition is met. A snort restart will typically interrupt active flows. Starting snort on an interface¶ click the snort interfaces tab to display the configured snort interfaces.
Snort can be deployed inline to stop these packets, as well. Substitute your own network ip range in. As a packet sniffer like tcpdump, as a packet logger — which is useful for network traffic debugging,.


![Basic Snort Rules Syntax And Usage [Updated 2021] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/032516_1127_SnortLabMan2.png)
![Basic Snort Rules Syntax And Usage [Updated 2021] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/032516_1127_SnortLabMan4.png)